DrayTek Vigor 2830v2 - 2830 VPN with Dynamic IP v4 Address
In this example we are looking at setting up a router for connecting a group of computers to a head office that may be behind another router or in a shared environment, often with a dynamic IP. In this example there is a Linksys router in front of the DrayTek at the satellite office over which we have no control. As a result we are setting the satellite office DrayTek Vigor 2830 to be a Dial-out only router and the head office Draytek 2830 to be receiving dial in only.
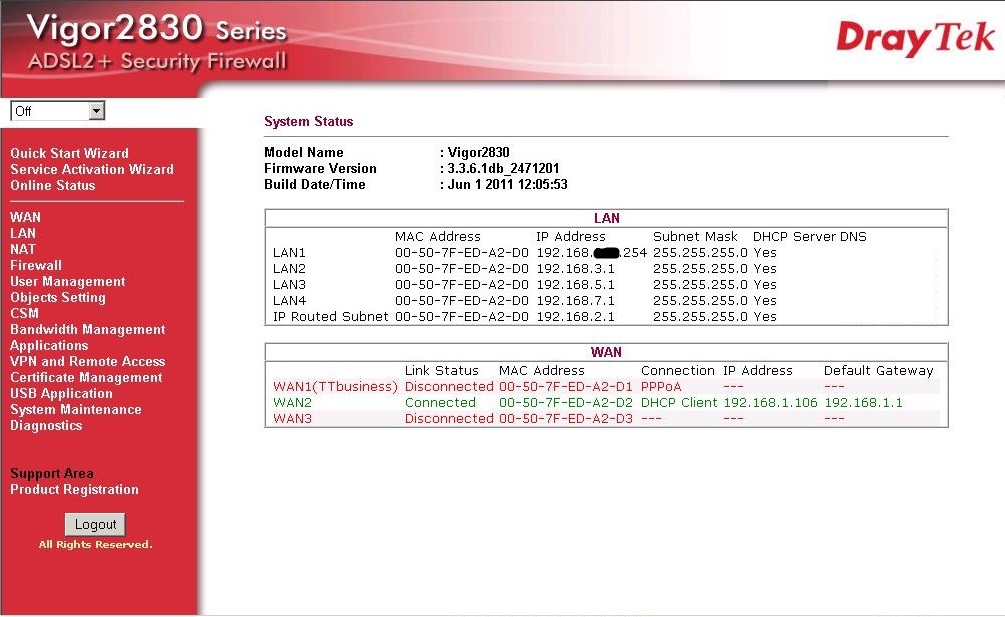
Firstly we log into the head office router to set up the incoming VPN settings...
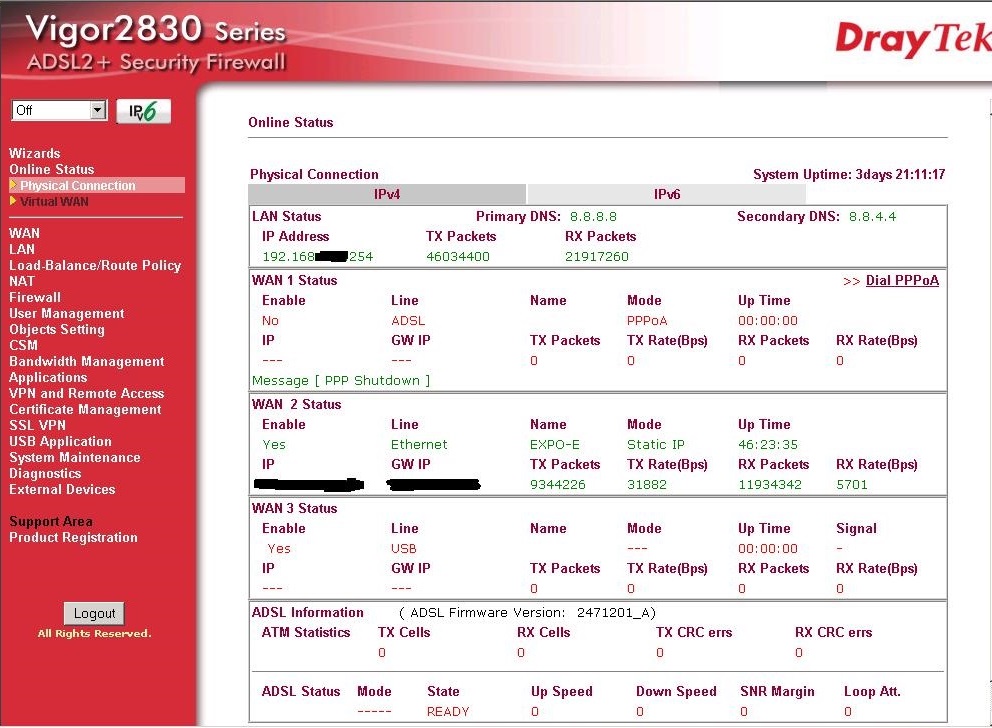
This router is on an ethernet circuit at head office - the WAN2 connection of this DrayTek handles synchronous 50 MB quite happily. Let's continue to the VPN section..
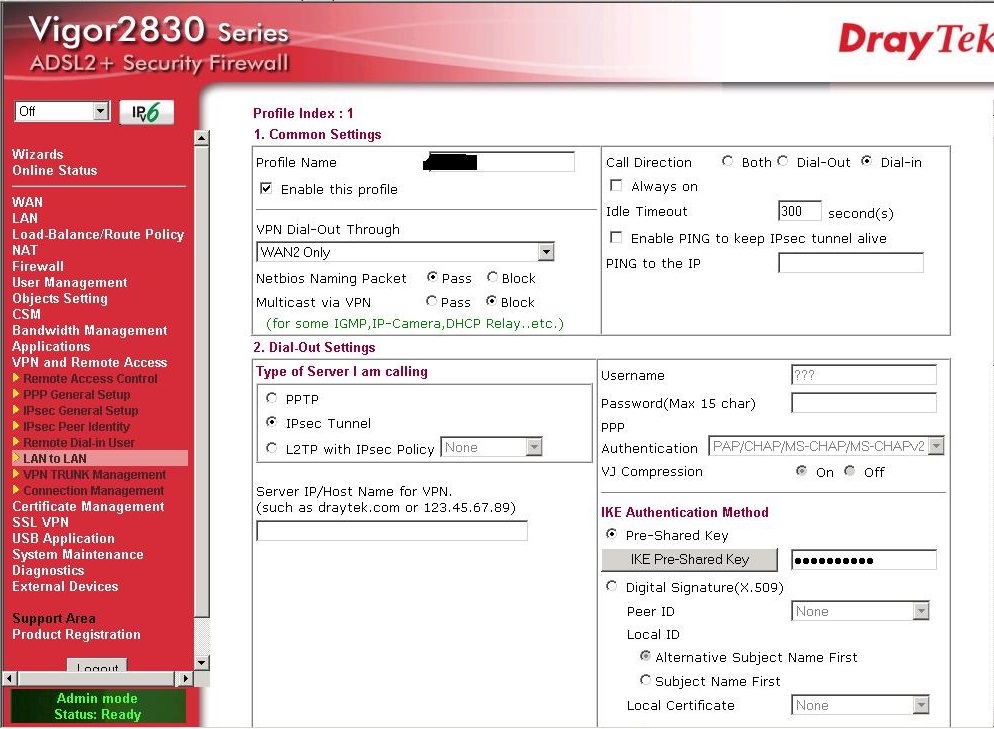
So we configure the system as dial-in and the VPN type to IPSec
we are not calling any device, only awaiting one to call us so we will leave the dial-out section unaltered with no hostname or IP address in the server box.
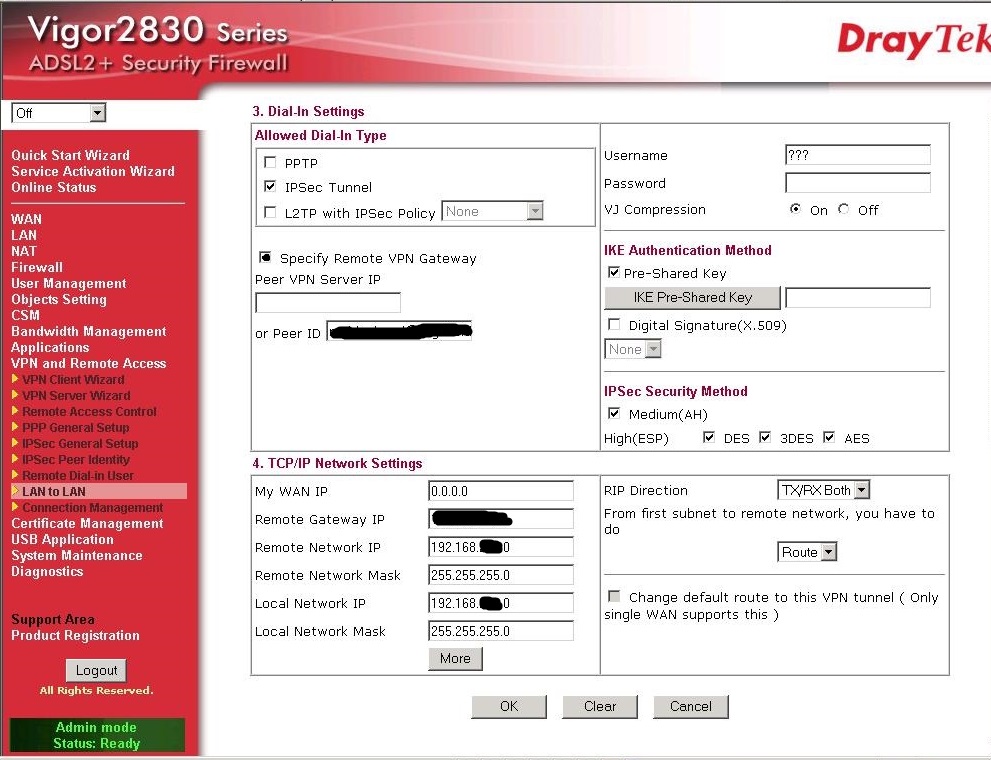
Now for the dial-in section. In here we must specify the details for accepting the VPN details from the satellite DrayTek:
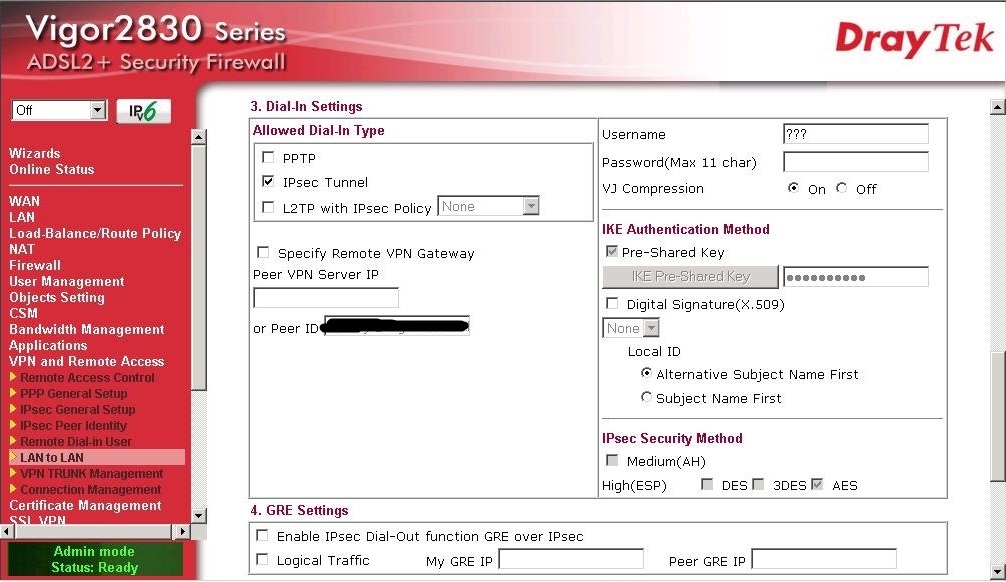
Once again we select IPSec as the VPN type. We do not add a username or password for IPSec. We will also leave the Peer ID blank.
We also leave section 4 - the GRE section - as default.
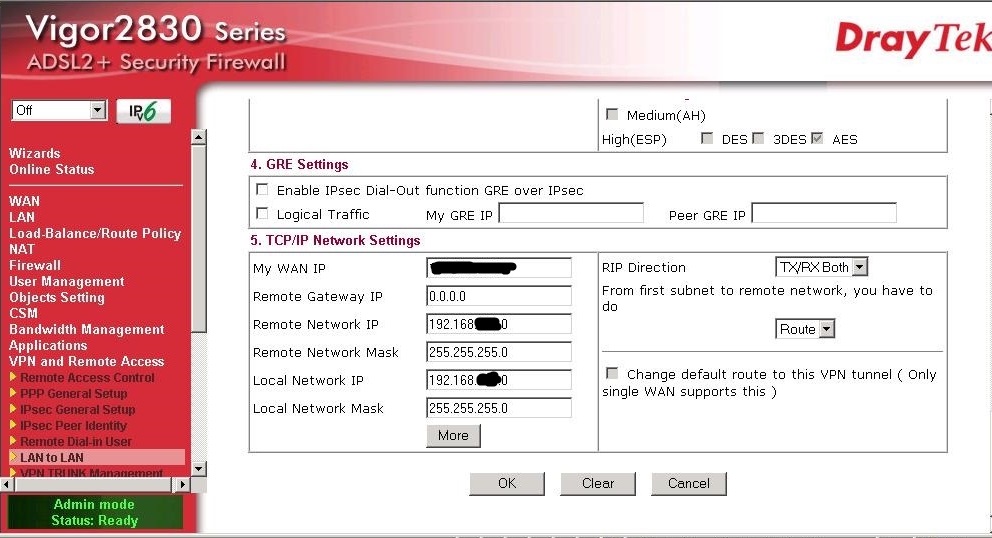
Here are the important settings for the LAN-LAN dynamic VPN - we must add our WAN IP which for the office is the routers IP on the ethernet network. You can see this on the original status page (example at the top of this post) as your routers WAN IP address.
The remote gateway IP stays as 0.0.0.0 as it will be dynamically changing in this example.
The remote network IP is the internal LAN subnet address - in this case a 192.168.x.0/24 address and so the subnet is 255.255.255.0 for a class C subnet.
The local network IP is the LAN subnet of the local LAN at head office. Again another 192.168.x.0/24 address - you must have configured the LAN on each router as a different range for successful routing. The local network mask is 255.255.255.0 again
Note the RIP settings are set to Tx/Rx and that we must Route to access the other side - this is important and must be set to Route not NAT
Finally we must set the Pre-Shared secret, which for a dynamic VPN we set under the VPN IKE/IPSec General Settings here:
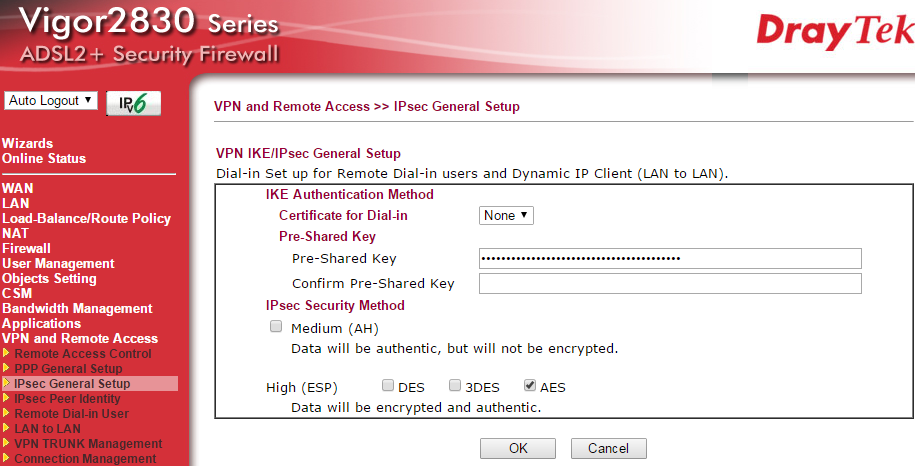
In this example we are using AES encryption and so we have ticked only that box.
Setting the Satellite VPN DrayTek Vigor
Once again we log into the DrayTek Vigor:
We head to the VPN section and the first available LAN-LAN profile:
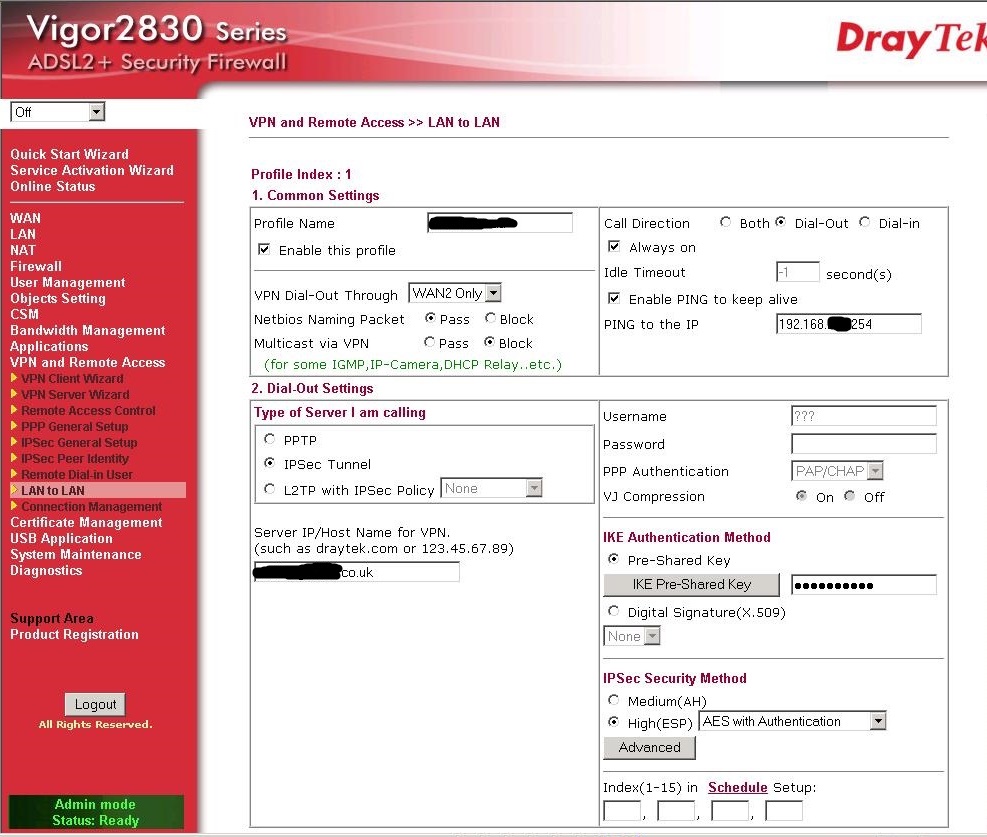
This time the router is set only to dial-out and we once again set the VPN type as IPSec and this time we are entering a PING to keep alive on the internal IP subnet of the remote LAN - in this case the router LAN address. This will enable us to keep the connection live and so allow for us to remotely administer machines etc. on that remote network. We have also ticked the 'Always On' box to help ensure this.
In our case the head office router has a URL we can add to point this router at the VPN endpoint but you may be using an IP address. Either way the external address of the head-office router you are connecting to goes there. You must also click the Pre-Shared Key button and enter the same shared secret as you entered in the IPSec General section on the Head office router, but there is no need to configure that page on this router as the IPSec Shared Secret we are using applies only to one tunnel, configured under the Lan-Lan section.
We are once again choosing AES with authentication as our VPN encryption to match the remote router. I have left the Phase 1 & 2 settings as default in this example as the shared secret is your security in this example and so I have elected not to change time-outs etc.
Now we are completing the IP settings, but for the opposite end of the VPN. Now our WAN IP is unknown and so it is left as the default, but the remote gateway is the same as the IP we entered earlier or is the IP address of the receiving routers WAN. The remote network IP is the LAN subnet of the other router and the local network IP is the local subnet, with the corresponding masks as before.
We keep the same settings for RIP direction and Routing for access.
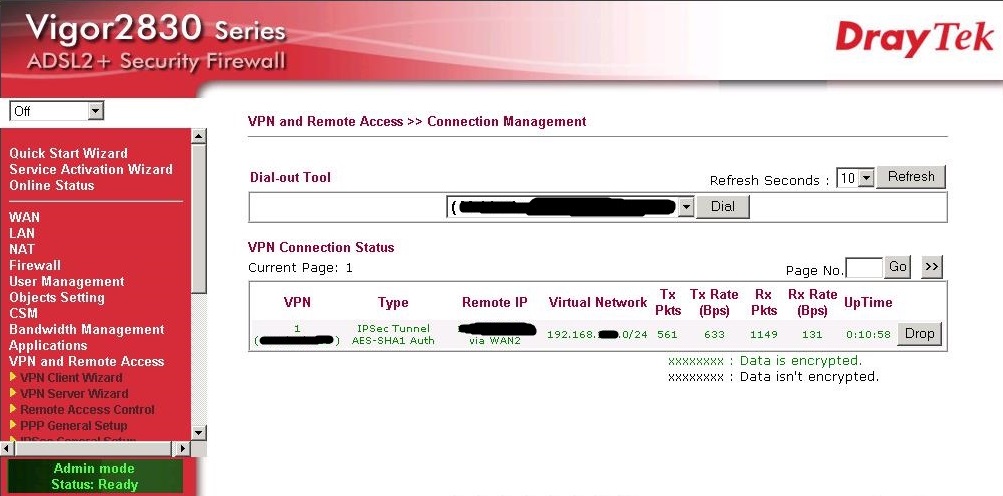
Now we have completed all of the settings required for a dynamic to static DrayTek VPN and so we can look at the VPN connection management tab just below where we are now: